FFT Pipeline Protection: Advanced Technologies to Safeguard Your Pipeline Infrastructure
Wiki Article
The Crucial Role of Information and Network Safety And Security in Shielding Your Information
In an age where information violations and cyber threats are significantly widespread, the value of robust information and network protection can not be overemphasized. The execution of effective security procedures, such as security and accessibility controls, is essential to preserving count on and functional honesty.Understanding Data Security
In today's digital landscape, an overwhelming bulk of companies grapple with the intricacies of information security. This crucial part of details technology includes safeguarding delicate data from unauthorized accessibility, corruption, or burglary throughout its lifecycle. Information protection encompasses numerous strategies and technologies, including security, accessibility controls, and information masking, all targeted at securing information against violations and susceptabilities.A basic aspect of data safety is the identification and category of data based upon its sensitivity and importance. This classification aids organizations prioritize their safety and security initiatives, designating resources to protect one of the most vital details effectively. Moreover, carrying out robust policies and procedures is vital to ensure that workers comprehend their role in keeping data protection.
Regular audits and analyses aid in identifying possible weak points within an organization's information safety framework. In addition, employee training is vital, as human error continues to be a significant factor in data violations. By promoting a society of safety recognition, companies can mitigate dangers connected with expert dangers and oversight.
Significance of Network Safety
Network protection stands as a foundation of an organization's overall cybersecurity technique, with about 90% of businesses experiencing some form of cyber danger over the last few years. The significance of network safety depends on its capability to safeguard sensitive information and maintain the integrity of organization procedures. By securing network frameworks, companies can avoid unapproved gain access to, data violations, and various other destructive tasks that might threaten their possessions and credibility.Executing durable network security determines not only aids in mitigating risks however likewise cultivates count on among stakeholders and clients. When consumers are ensured that their individual and economic details is protected, they are more probable to involve with the organization, leading to boosted client loyalty and business growth.
In addition, a well-structured network safety and security structure assists in compliance with numerous governing needs. Organizations has to stick to sector standards and lawful requireds worrying data protection, and reliable network protection techniques can make certain conformity, therefore avoiding potential penalties.
Typical Cyber Hazards
Organizations should stay watchful against a range of cyber dangers that can threaten their network protection efforts. Among one of the most common hazards is malware, which includes viruses, worms, and ransomware that can disrupt procedures, swipe information, or hold information captive. Phishing strikes, where harmful stars impersonate trusted entities to trick people right into revealing sensitive info, remain to grow in sophistication, making individual education and learning critical.Another prevalent danger is distributed denial-of-service (DDoS) assaults, which overload systems with traffic, providing them inaccessible to legit users. Insider hazards, whether unexpected or willful, present considerable threats as employees may unintentionally reveal sensitive information or intentionally exploit their access for destructive objectives.
In addition, vulnerabilities in software and equipment can be manipulated by cybercriminals, highlighting the relevance of routine updates and patch administration. Social design methods additionally complicate the landscape, as opponents control individuals right into divulging personal info through psychological manipulation.
As these threats develop, companies must preserve a positive strategy to recognize, mitigate, and react effectively to the ever-changing cyber threat landscape, protecting their useful info and preserving trust fund with stakeholders. fft pipeline protection.
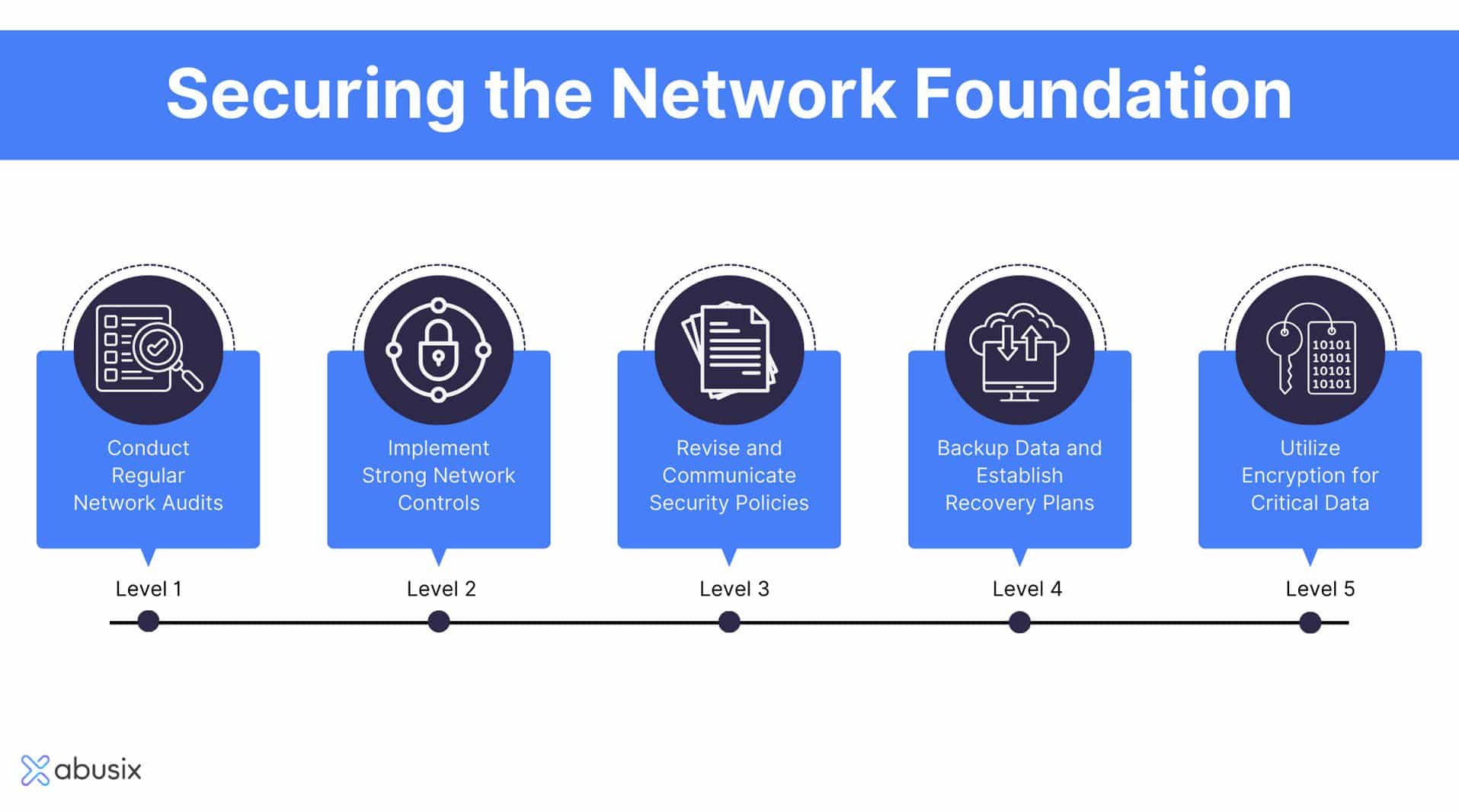
Finest Practices for Protection
Carrying out durable security steps is important for protecting delicate information and keeping operational stability. Organizations should start by performing comprehensive danger assessments to recognize susceptabilities within their systems. This positive strategy makes it possible for the prioritization of safety and security initiatives tailored to the certain requirements of the company.Adopting strong password plans is crucial; passwords should be complex, on a regular basis altered, and took care of making use of protected password administration devices. Multi-factor verification (MFA) adds an added layer of security by requiring added verification techniques, thus minimizing the danger of unauthorized gain access to.
Routine software application updates and patch administration are vital to secure versus understood vulnerabilities. Carrying out firewall softwares and breach detection systems can better protect networks from outside dangers. Employee training is equally crucial; staff needs to be educated on recognizing phishing attempts and understanding the significance of information safety methods.
Information encryption must be used for delicate info, both at rest and en route, to make certain that even if data is intercepted, it stays hard to reach (fft pipeline protection). Organizations must establish and frequently examination event reaction intends to guarantee speedy activity in the event of a safety breach. By sticking to these finest methods, organizations can boost their security posture and safeguard their critical information possessions
Future Trends in Safety And Security
The landscape of information and network safety and security is continually advancing, driven by improvements in innovation and the raising elegance of cyber threats. As companies significantly embrace cloud computer and IoT gadgets, the paradigm of security will change toward a zero-trust design. This approach highlights that no entity-- outside or internal-- is naturally trusted, mandating verification at every accessibility point.In addition, making use of synthetic intelligence and equipment knowing in safety methods is on the increase. These innovations enable predictive analytics, permitting companies to identify vulnerabilities and prospective hazards prior to they can be exploited. Automation will likely play a crucial function in improving security feedbacks, reducing the moment required to reduce violations.
Furthermore, regulatory structures will proceed to tighten up, necessitating extra rigorous conformity steps. Organizations must stay abreast of progressing guidelines to ensure they meet safety and security standards.
Final Thought
To conclude, the relevance of information and network security can not be overemphasized in the modern electronic landscape. With the prevalence of cyber hazards and the boosting intricacy of regulative needs, organizations should take on comprehensive security measures to secure delicate information. By remaining and executing reliable strategies educated concerning emerging trends, services can enhance their strength against potential assaults, making sure information honesty and promoting count on among customers and stakeholders. Focusing on safety and security continues to be essential for functional connection and long-lasting success.In a period where information breaches and cyber dangers are increasingly common, the relevance of robust information and network security can not be overstated. data and network security Data safety incorporates numerous approaches and modern technologies, consisting of file encryption, accessibility controls, and information masking, all intended at guarding info against violations and vulnerabilities.
A basic aspect of data safety and security is the identification and category of data based on its sensitivity and value.The landscape of data and network safety and security is constantly evolving, driven by developments in modern technology and the enhancing class of cyber dangers.In verdict, the importance of information and network safety can not be overstated in the contemporary electronic landscape.
Report this wiki page